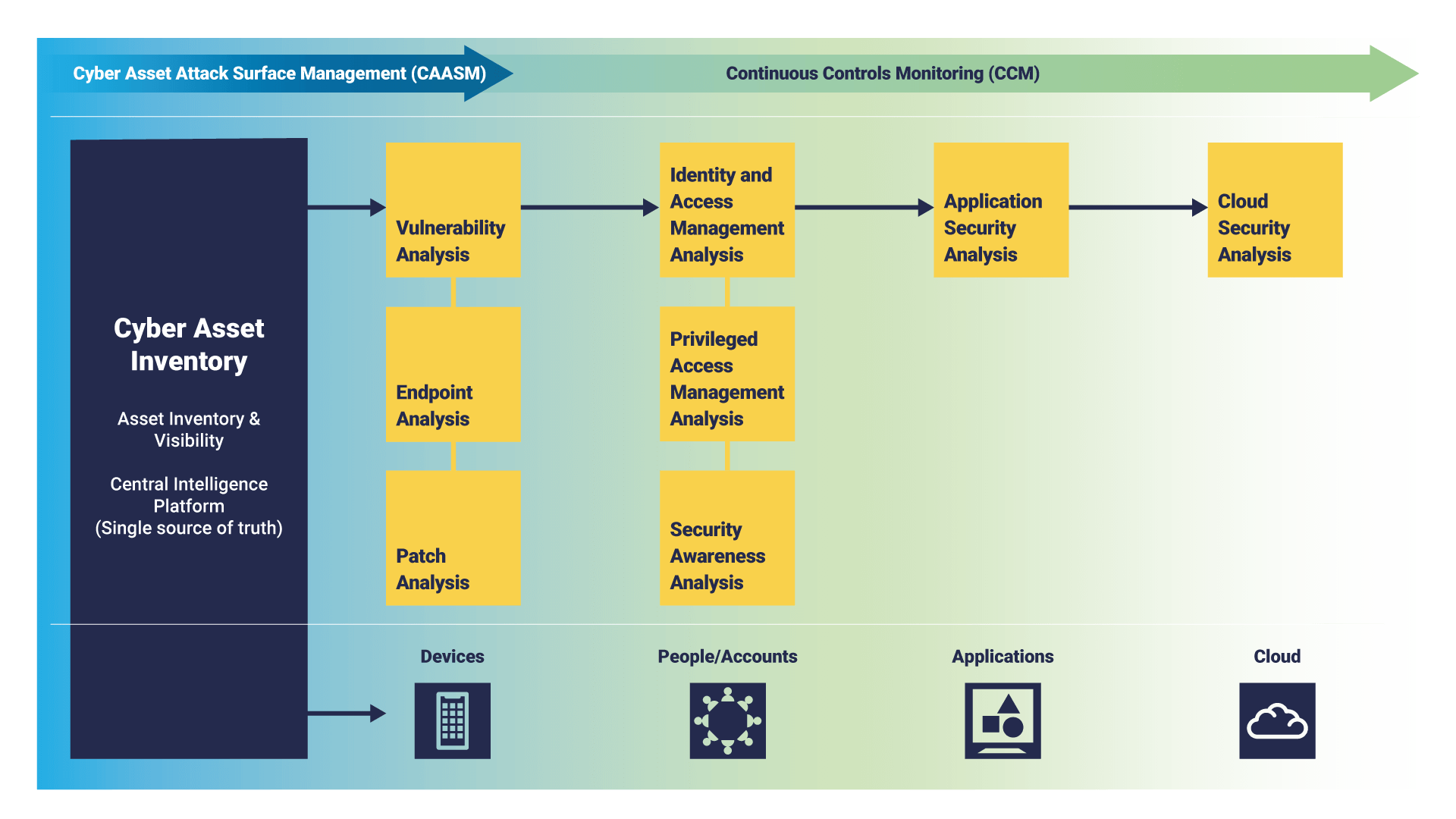
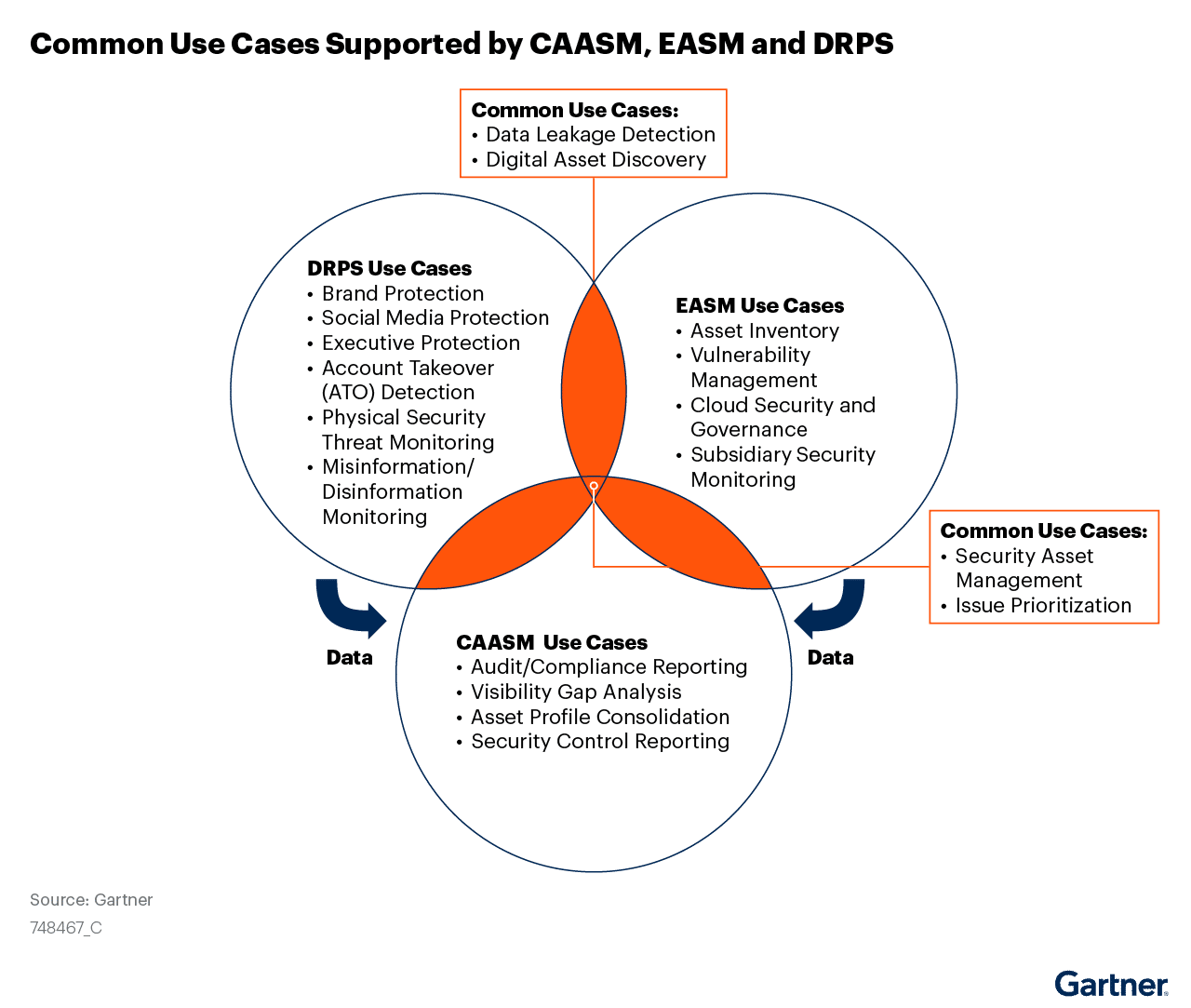
How to Use Cyber Asset Attack Surface Management (CAASM) Technology to Gain Complete Visibility of Assets - Apexa IQ

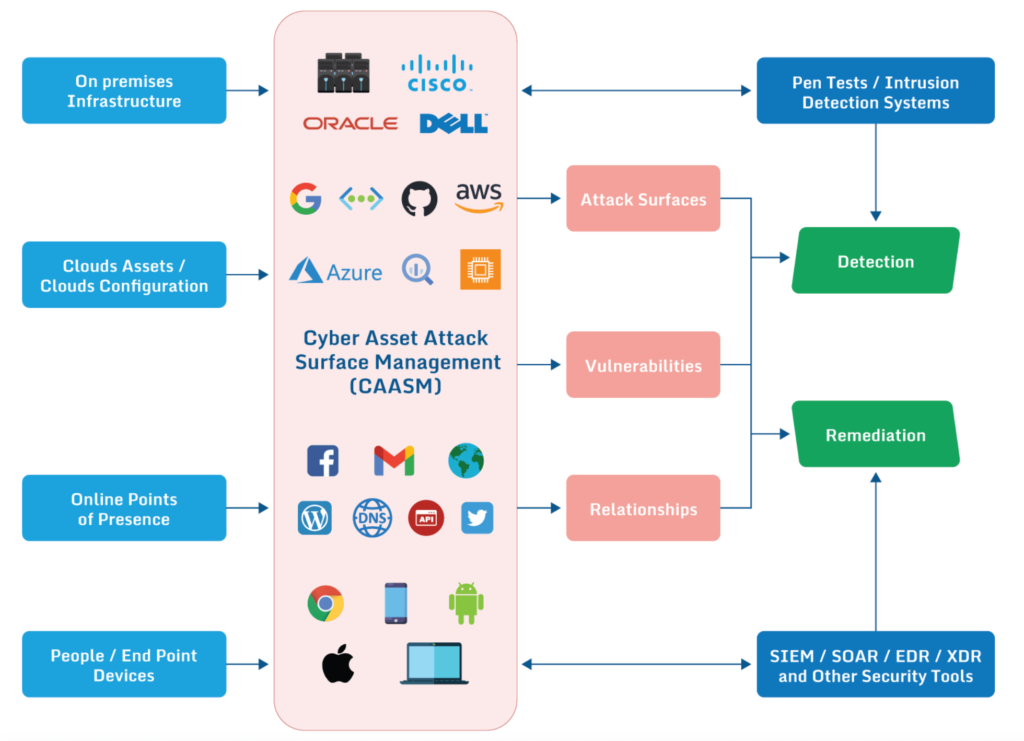
The Importance of Scanning Sources in CAASM: Why Management Tools Aren't Enough | by Lansweeper Embedded Technologies | Medium

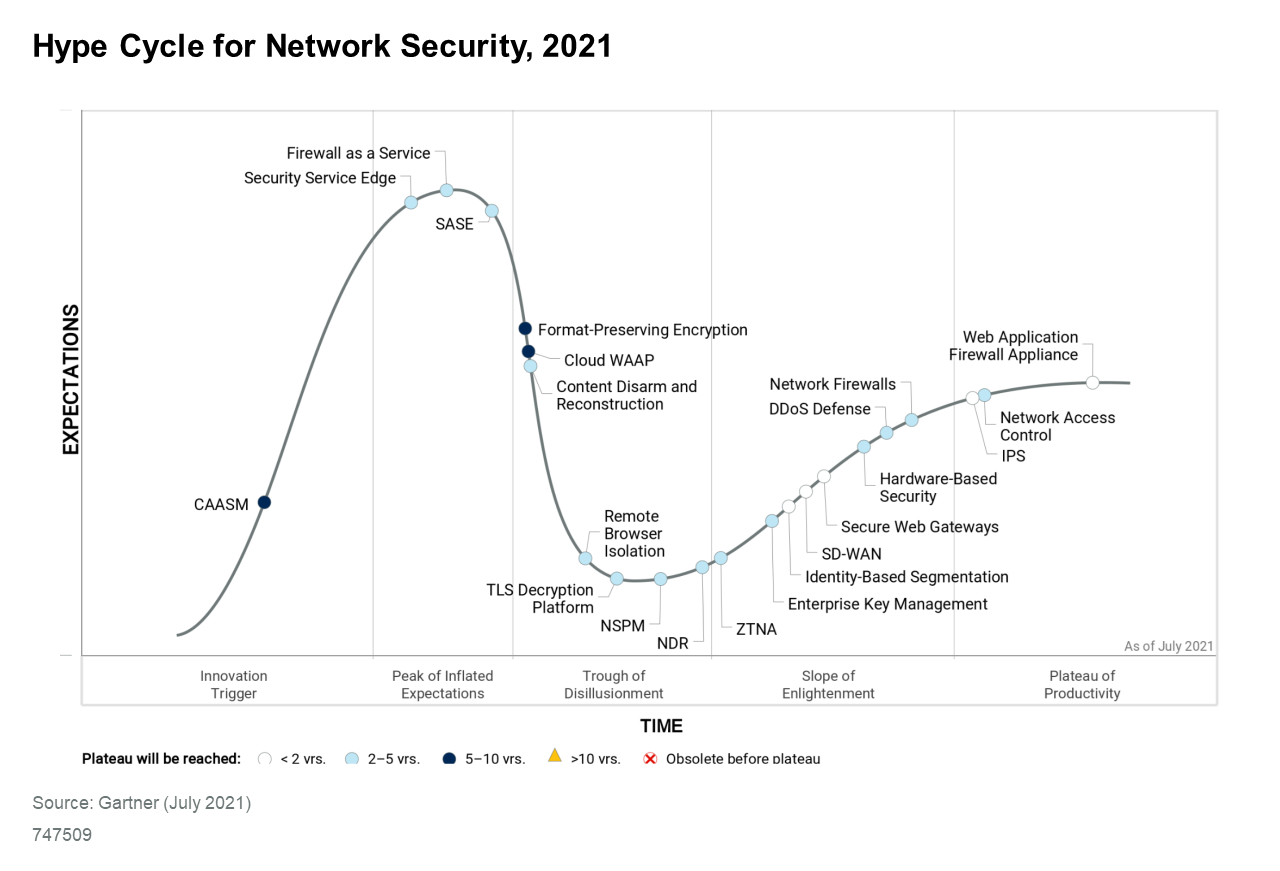
RSAC insights: 'CAASM' tools and practices get into the nitty gritty of closing network security gaps | The Last Watchdog