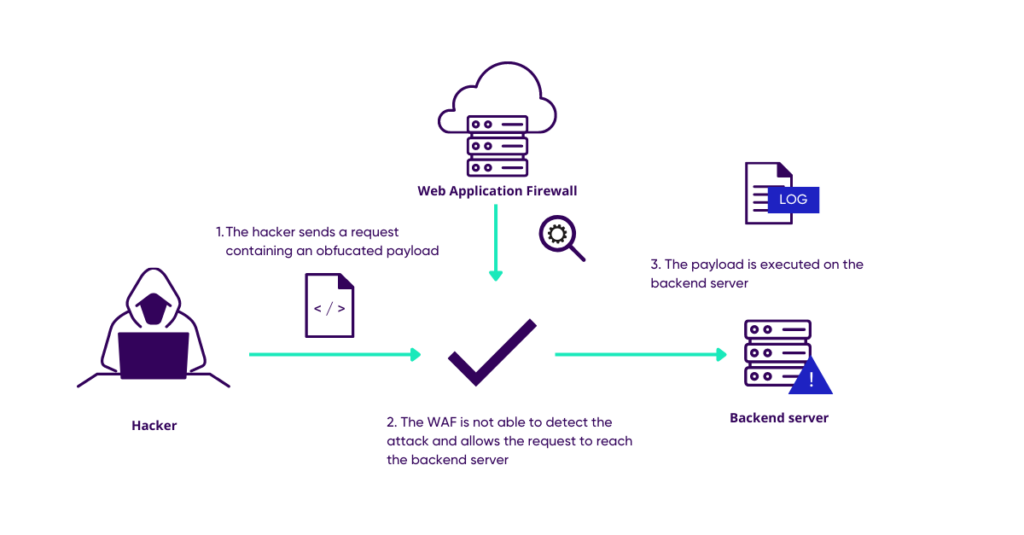
Obfuscation in Android. The process of modifying an executable… | by Supun Ishara Weerasekara | Level Up Coding
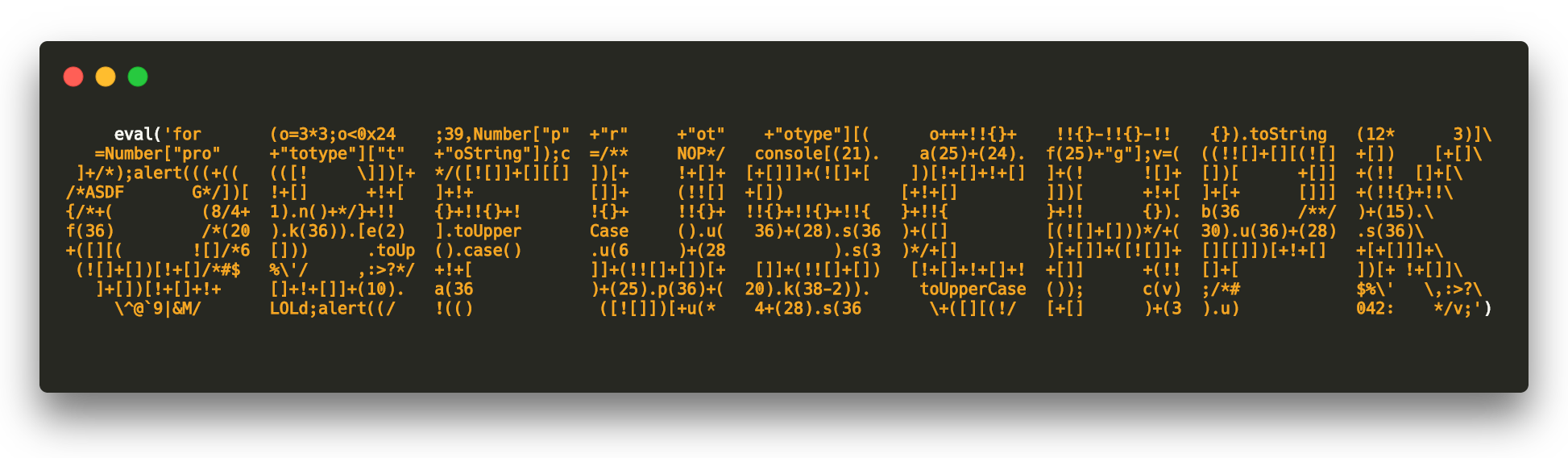
GitHub - ClaudiuGeorgiu/Obfuscapk: An automatic obfuscation tool for Android apps that works in a black-box fashion, supports advanced obfuscation features and has a modular architecture easily extensible with new techniques

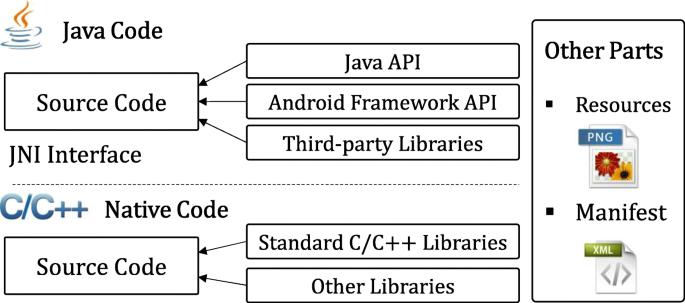
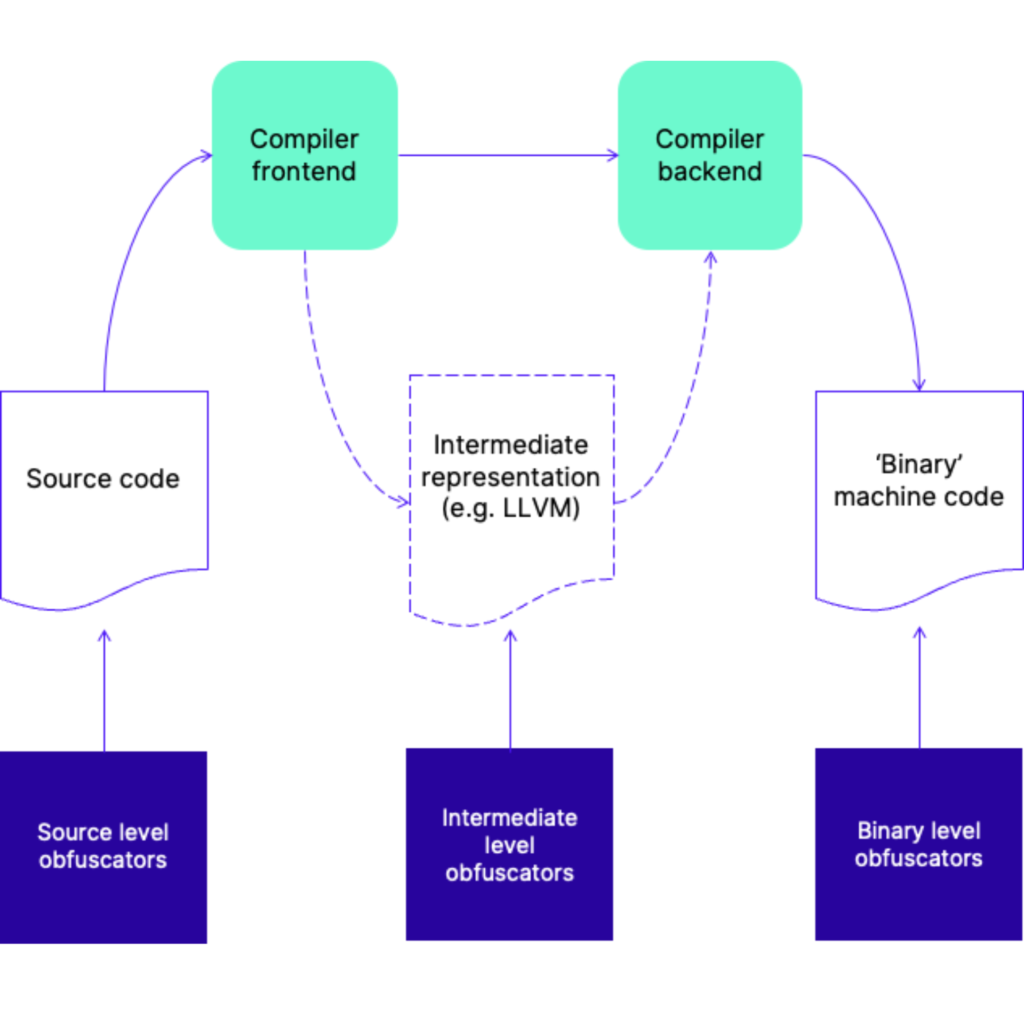
Layered obfuscation: a taxonomy of software obfuscation techniques for layered security | Cybersecurity | Full Text